Intrusion + Life Safety
Alarm zones and fire detection are tuned for early warning while reducing false signals.

Integrated Security Operations
Yale Security Systems designs layered protection programs where intrusion, fire, surveillance, and access control work as one response system.


Monitoring Status
24/7 LIVE7+ Years of Service
1000+ Properties Protected
99.9% System Uptime
24/7 Monitoring Coverage
Response Method
We run every project through a repeatable command flow so your security stack is engineered, tested, and maintained with clear accountability.


Threat map and operational risk discovery.
Layered architecture for alarm, fire, video, and access.
Certified commissioning and scenario testing.
24/7 signal supervision and event verification.
Routine audits, updates, and reliability checks.
Emergency coordination and post-incident review.
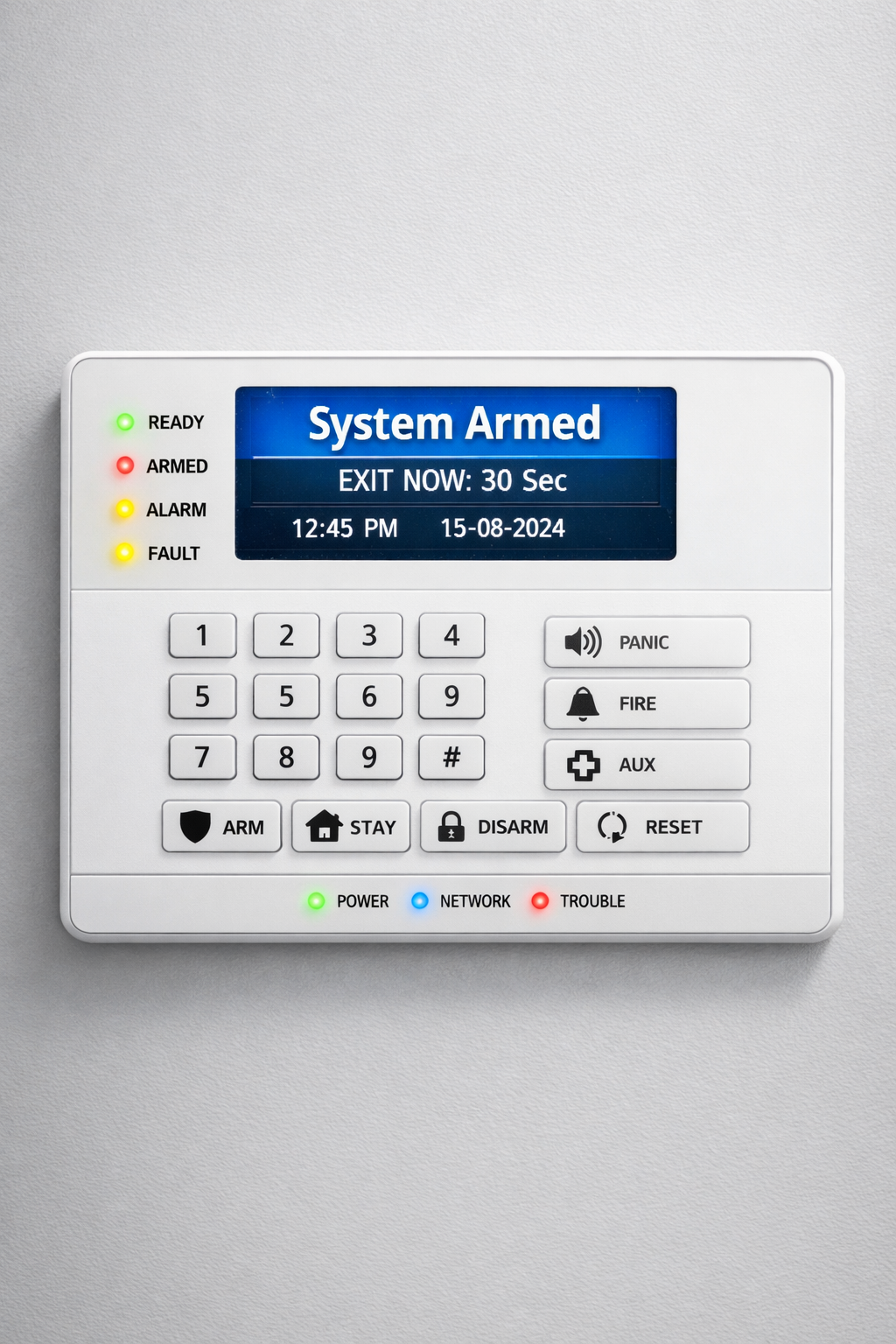
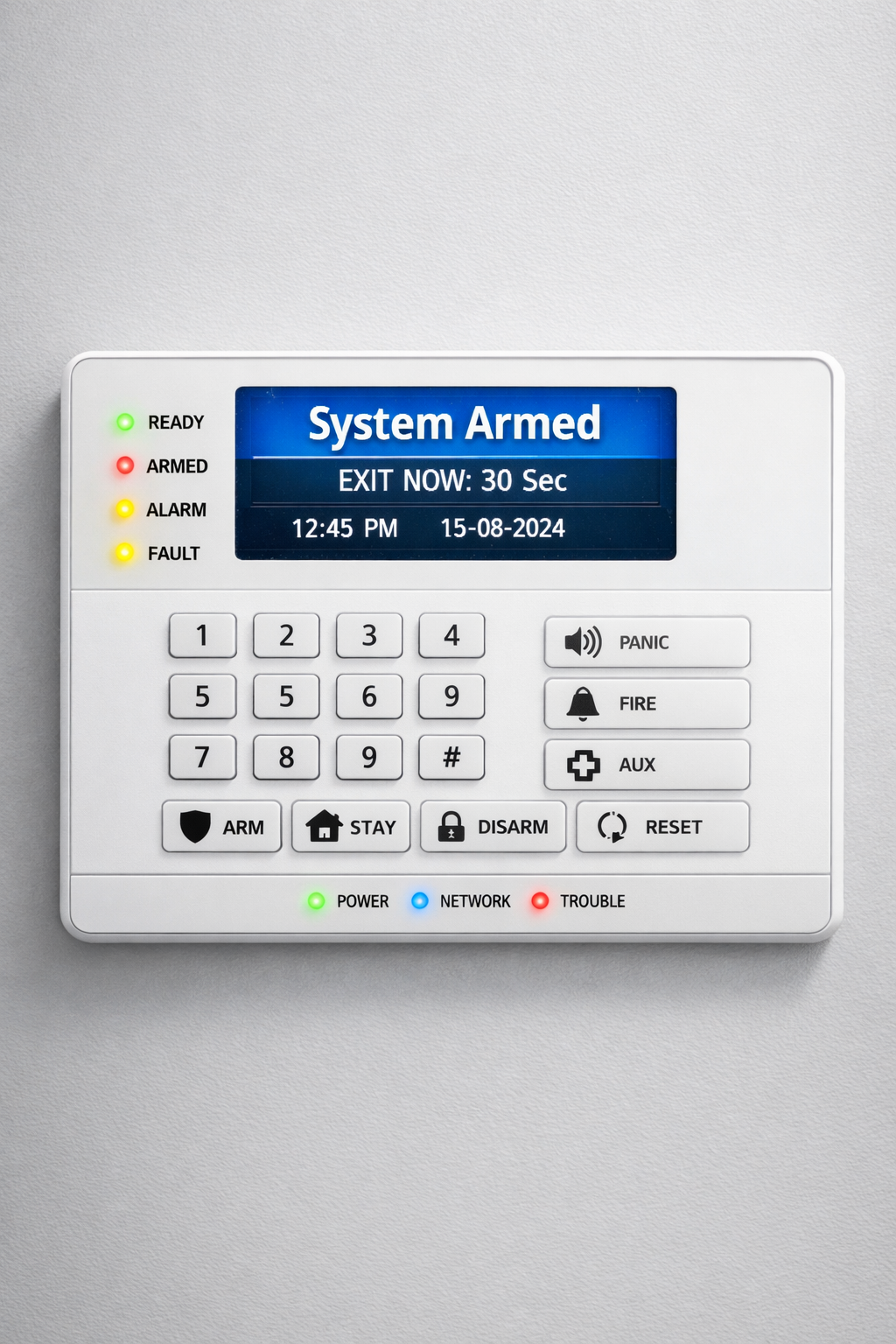
Operations Wall
The work is continuous: technicians in the field, analysts in the monitoring room, and response teams aligned to act fast.









Security Architecture
Each layer is engineered to exchange context so teams can verify incidents faster and respond with confidence.
Alarm zones and fire detection are tuned for early warning while reducing false signals.

Camera coverage and perimeter controls provide visual verification before escalation.



Entry controls and alert intelligence keep movement traceable and event context clear.




Mobile command and wireless hardware keep users connected to security status anywhere.



Deployment Coverage
We adapt by property type while keeping one standard for monitoring rigor, maintenance quality, and incident escalation.
Family-focused protection with remote visibility and low-friction daily use.
Audit-ready security operations for offices, retail, and multi-site facilities.
Direct Contact
Share your property profile, current system limitations, and risk priorities. Our team will outline a phased deployment strategy.